Dear friends, sharing with you mnemonic words for CHAPTER 3 of ISCA.
Word file of same is also uploaded in files section of the site. Click here
ISCA - CHAPTER 3
Reasons for Gap between Need to protect system and protection applied : HIDE & U C ME (Prof. Jignesh Chheda)
- External dangers from Hackers
- Inter connectivity of systems
- Devolution of management & control
- Elimination of Time, Distance, Space constraints
- Widespread Use of technology
- Unevenness of technological Changes
- Growing potentials fir Misuse
- External factors such as legal & regulatory requirements
IS Security:
- Protection of valuable assets from threat, sabotage etc.
- IS security can be > Physical e.g. Locks, Insurance > Logical / Technical e.g. Passwords, Firewalls
- To be Holistic - applies to all information to be protected.
IS Security Objectives : To Protect -
- Interest of those relying of Information
- Information system that delivers information
Attributes of IS Security Objectives : CIA = u (DMW) (Prof. Jignesh Chheda)
- Confidentiality : To Prevent - unauthorized Disclosure
- Integrity : To Prevent - unauthorized Modification
- Availability : To Prevent - unauthorized Withholding
What Information is Sensitive : SBF
- Strategic Plans : > Crucial for the success of the company > Gives Competitive advantage to competitors if reached their hands
- Business Operations : > Processes & procedures that are proprietary in nature e.g .Price List, Formulae etc. > Damaging if passed on in hands of competitors
- Finance : > Financial Information such as Salary & wages > Range known within the Industry but precise information gives competitive advantage to others
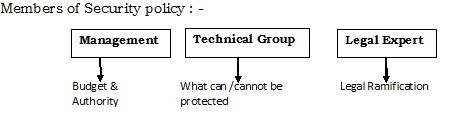
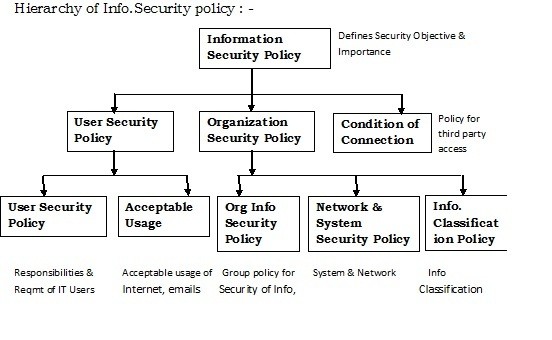
Information Security policy :
- Statement of Intent by the management on how to protect information and assets
- Does not specify Technology but give rules to - i) Protect information from unauthorized DMW ii) Eliminate Legal liabilities iii) Prevent waste of resources
- It must be in written form
Tools to Implement Security policy :
- Standards : > Specify Technology to be implemented
- Guidelines : > Helps smooth implementation of policy
- Procedures : > Gives detailed steps to be followed to achieve goals > Assist in implementation of policy
Issues to address by Security policy : DIG Beats Right hand of Dawood
- Definition of Information security
- Importance of Information security to the organization
- Goals and Objectives Information security
- Brief explanation of security policies, principles, standards
- Definition of all relevant security Responsibilities
- Reference to supporting Documentation
Auditor’s responsibilities in Security policy: Auditor should ensure that policy -
- Available to all employees
- Employees are aware of its existence
- Has a owner responsible for maintenance
- Updates for any changes
Components of Security Policy : PSI IPS AT IB In Legal Monitoring Dept.
- Purpose & Scope of the document
- Security Organization Structure
- IT operations management
- IT Communications
- Physical & Environmental security
- System development & maintenance
- Access Control
- The security Infrastructure
- Incident Handling
- Business Continuity Planning
- Inventory & Classification of assets
- Legal Compliance
- Monitoring & auditing requirement
- Document maintenance & compliance
IS Controls :
Need for IS Controls -
- Tremendous amount of data and information due to technology
- Timely flow of accurate information Requires built in controls
IS Control procedures : SAS O Q Pite Bahu and Pati
- Strategy and direction
- Access to IT Resources, Data & Program
- System development methods and change control
- Operation procedures
- Quality Assurance procedures
- Physical Access control
- BCP & DRP
- Protective and Detective mechanism
Impact of Technology on Internal Controls : MARS is At Peak Into Darkness (Prof. Jignesh Chheda)
- Management Supervision
- Access to Assets and Records
- Record keeping
- Segregation of duties
- Authorization procedures
- Personnel
- Independent Check
- Delegation of authority
5 Inter-related components of Internal Control : ReMA Is a nice girl (Prof. Jignesh Chheda)
- Risk Assessment
- Control Environment
- Monitoring
- Control Activities
- Information & Communications
IS Control Techniques :
Objectives of Controls :
- Controls defined as Policy, Procedure, Practices and Organization structure designed
- To provide reasonable assurance that business objective will be met and undesirable events will be prevented
- Reduce or Eliminate cause of Exposure
Critical Control Considerations : LAB CT scan
- Lack of management understanding of IS Risk and Controls
- Absence or weak IS Control
- Lack of awareness of IS Risks among Business users
- Complexity in implementing controls
- Lack of implementation of controls in highly Technology driven environment
Purposes met by Controls objectives : OB
- Outline policies laid down by management
- Benchmark to evaluate whether controls objectives are met
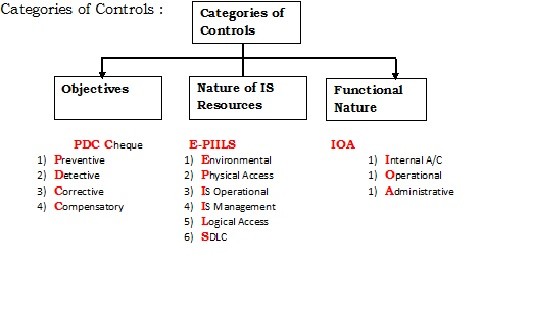
Preventive Controls :
Characteristics : VP Control
- Understanding Vulnerabilities of assets
- Understanding Probable threat to assets
- Provision of Controls against probable threat
Example : > Segregation of duties > Anti-Virus > Passwords
Detective Controls :
Characteristics : RP Singh
- Report unlawful activities to appropriate person
- Prevent such acts from occurring
- Surprise checks by Supervisor
Example : > Hash totals > Intrusion Detection system > Bank Reconciliations
Corrective Controls :
Characteristics : MIC Man
- Minimize impact of threat to assets
- Identify the cause of problem
- Correcting error arising from problem
- Modify the processing system to minimize further occurrence of problem
Example : > Contingency Plan > Back up procedure > Return procedure
Organizational Controls Techniques : RP Job Search
- Definition of Responsibilities & Objectives of each function
- Policies and Procedures
- Job description
- Segregation of duties
Management Controls : MIS - File
- By the Management to ensure system functions correctly
- IT activities are adequately controlled
- Scope of controls includes framing high level IT policies, standards and establishing Internal Controls
- Controls Flows from Top to Down in organization
Financial Controls : ABCD2 Sequel -2 (Prof. Jignesh Chheda)
- Authorization
- Budget
- Cancellation of Documents
- Documentation
- Dual Control
- Safe keeping
- Sequentially numbered documents
Boundary Control techniques : Cryptography In Pin Password
- Cryptography
- Identification Cards
- Personal Identification No. (PIN)
- Password
Update Controls : Sanjay Elected MP
- Sequence Check Transaction and Master files
- Ensure all record files are processed
- Maintain Suspense account
- Process multiple transactions for single record in correct order
Report Controls : Priyanka Sonia Rahul (PSR)
- Print Run-to-Run Control
- Standing Data
- Recovery Controls
Information Classification :
Information classification should be based on level of sensitivity i.e. extent to which to information needs to be protected.
5 Grades of Information Classification: Tu Hai Pehla Intezar aur Pyaar
- Top Secret
- Highly Confidential
- Proprietary
- Internal Use only
- Public documents
Data Integrity :
Data Classified should be secured through various data integrity controls. Data Integrity is reflection of accuracy, correctness and validity of data
Objectives of Data Integrity
- To prevent, detect, correct errors in transactions through stages of processing
- To protect data from accidental / malicious alteration
Critical procedures in assessing Data Integrity
- Virus detection and elimination through installation of software
- Validation controls to provide assurance that information not altered
Six categories of Data Integrity controls : Shine In Old POT
- Source data control
- Input validation routines
- Online data entry control
- Processing and Storage of data control
- Output control
- Transmission of data control
Data Integrity Policies : Vijay Sales takes Daily Backup of Data (Prof. Jignesh Chheda)
- Virus Signature updating
- Software testing
- Division of Environment
- Offsite Backup storage
- Backup storage -quarter end / year end
- Disaster recovery
Logical Access Control :
Logical Access Paths : TODO (Prof. Jignesh Chheda)
- Telecommunication Network
- Online Terminals
- Dial up Ports
- Operator Console
Issues and Exposures to Logical Access :
A] Technical Exposure - Sachin Ramesh Tendulkar Batting Technique During World cup
- Salami Technique
- Rounding Down
- Trap Doors
- Bombs - Time & Logic Bombs
- Trojan Horse
- Data Diddling
- Worms
B] Computer Crime Exposure - F -DISCS (Prof. Jignesh Chheda)
- Financial Loss
- Disclosure of Confidential & Sensitive Information
- Industrial Espionage / Blackmail
- Sabotage
- Credibility Loss
- Spoofing
C] Asynchronous Attacks - Pen Drive Wirus Scan
- Piggybacking
- Data Leakage
- Wire Tapping
- Shut Down / Denial of Service
User Access Control :
User Access Management : UP Under Review
- User Registration
- Privilege Management
- User Password Management
- Review of user access rights
User Responsibilities : UP
- Unattended user equipment
- Password Use
Operating system Access Control : TU Padh Direct Tax Laws
- Automated Terminal Identification
- User Identification and authentication
- Password Management system
- Duress alarm to safeguard users
- Terminal Time Out
- Limitation of connection time
Physical Access Control : Amitabh Bachchan Payment DUE
Issues and Exposures to Physical Access :
- Abuse of data
- Blackmail
- Public disclosure of sensitive information
- Damage, Vandalism
- Unauthenticated entry
- Embezzlement
Possible Perpetrators to Physical Access : GOINg DEAF (Prof. Jignesh Chheda)
- Gambling addiction
- On Strike
- Information to competitors, thieves, hackers,
- Notified on Termination
- Dissatisfied
- Threatened by Disciplinary action
- Emotional problems
- Accidental Ignorant
- Former employee
Access Control Mechanism 3steps : India - Afghanistan Agreement
- Identification
- Authentication
- Authorization - 2 approach - a) Ticket Oriented b) List Oriented
Cyber Frauds : Frauds committed by the use of technology
Major reasons for increase of frauds : IOS
- Internal Control failure
- Organizations failure to update to new set of risks
- Smart fraudsters who target weakness in system before organization realizes
Types of cyber frauds based on functionality : PC
- Pure cyber frauds
- Cyber enabled frauds
Major cyber attacks : WE Started New SPV
- Website compromise
- Eavesdropping
- Scavenging
- Network scanning
- Spam
- Phishing
- Virus / malicious codes
Impact of cyber frauds on Enterprise : FD Loss Legal Stand
- Financial Loss
- Disclosure of Sensitive Information
- Loss of Credibility
- Legal Repercussion
- Sabotage
Techniques to Commit cyber frauds:
- Hacking
- Cracking
- Data Diddling
- Data Leakage
- Denial of Service attack
- Logic / Time Bomb
- Masquerading
- Round Down
- Scavenging














 CAclubindia
CAclubindia
